Attack Surface Management vs Vulnerability Scanning: What’s the Difference?

A simple guide for understanding how ASM actually supports your security program.
We often hear organizations ask:
“How is Attack Surface Management (ASM) different from vulnerability scanning?”
Here’s the straightforward answer.
What Vulnerability Scanning Does
Vulnerability scanning checks your known systems for known weaknesses – missing patches, outdated versions, misconfigurations, and published CVEs.
It’s great for:
- Cybersecurity hygiene
- Compliance requirements
- Patch validation
- Detecting issues on systems you already track
But vulnerability scanning cannot:
- Identify unknown or unmanaged assets
- Tell you if your security controls are working as intended
- Show how internal systems are interconnected
- Help prioritize what matters in a practical, operational way
- Detect changes in your environment over time without manual effort
Scanning gives you important information, but only about the assets you already know exist.
What Attack Surface Management Does (Sedara’s Inside-Out Approach)
Sedara’s ASM focuses on what’s happening inside your environment – how your systems behave, how your controls function, and where exposures exist based on internal telemetry and existing security applications.
Think of it as validating what your tools and teams believe is happening, versus what is actually occurring within your environment.
ASM helps you understand:
ASM helps you understand how your environment behaves and where exposures emerge. The concept of attack surface management is also explained by CISA.
- Which assets and identities actually exist
- Where controls are behaving differently than expected
- How exposures emerge due to drift, misconfiguration, or change
- What should be addressed first based on operational impact
- Where gaps form between policy, configuration, and reality
ASM gives you clarity and confidence in your internal environment — not another list of vulnerabilities, but a better understanding of exposure and misalignment.
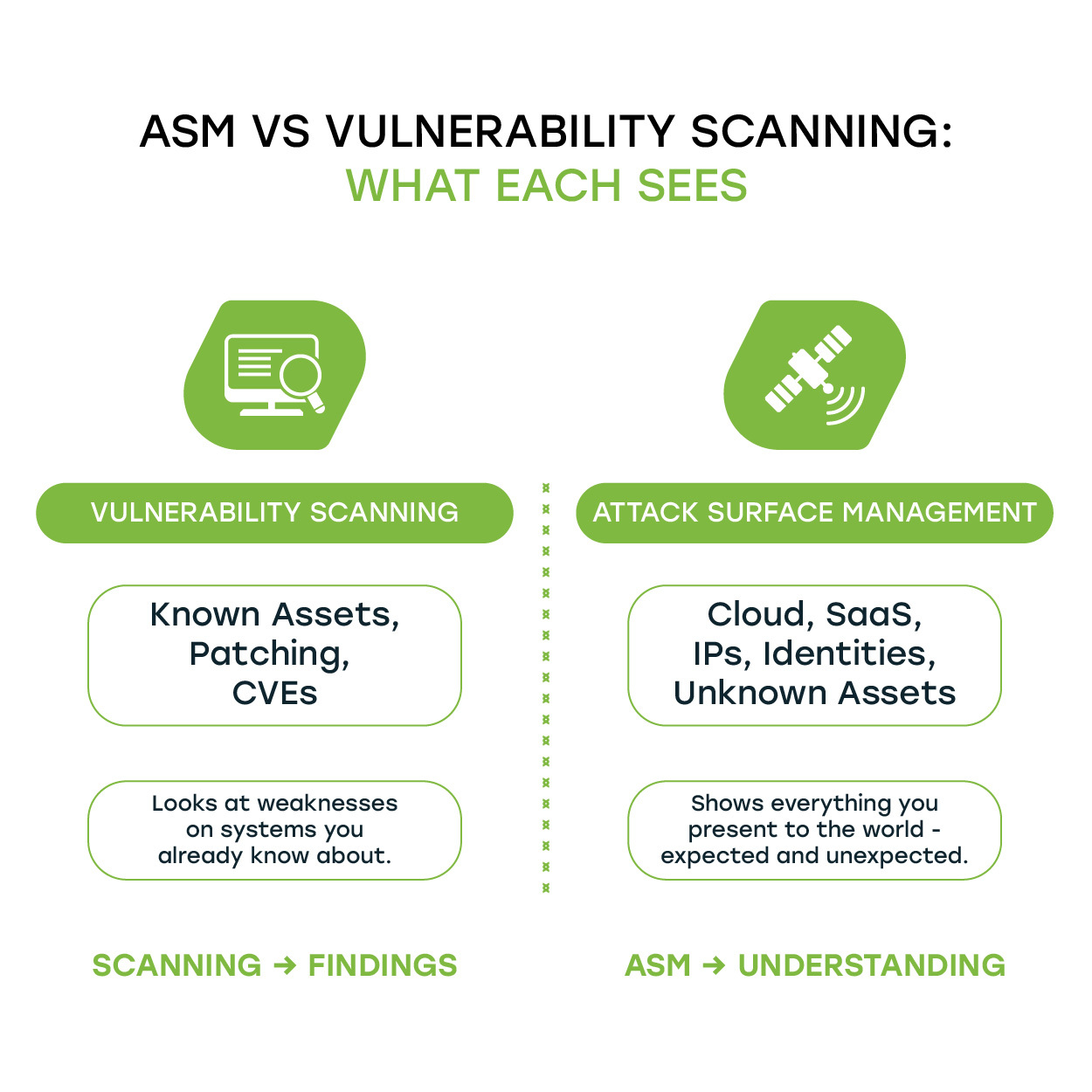
The Core Difference: Findings vs. Understanding
Many organizations are already overwhelmed with findings.
What they lack is context.
Vulnerability Scanning = Findings
A list of weaknesses is usually large and difficult to prioritize.
Attack Surface Management = Understanding
A clearer view of where exposures come from, why they matter, and what to address first.
ASM isn’t a replacement for vulnerability scanning; it serves a different, equally important role.
How ASM and Vulnerability Scanning Work Together
Both support your security goals, but in different ways.
- Scanning improves hygiene by identifying known issues on known systems.
- ASM strengthens confidence by showing where your environment doesn’t match expectations.
Together, they give you a far more accurate picture of your true risk.
Want clarity around your environment and exposure?
If you’d like help understanding how ASM fits into your security program or how to build more confidence around what’s happening in your environment, we’re here when you need us.
Learn more about Sedara’s Attack Surface Management Approach.