
Our Security Management Appliance Helps With Assessments and Vulnerability Management
The SMA provides Assumed Breach Capabilities, IDS, Vulnerability Scanning, Log Collection, Network Monitoring, and Penetration tool sets.
Assumed Breach Capabilities and Simplified Administration
Cyber criminals continue to breach companies with ever-evolving techniques. Today, many organizations focus only on perimeter defenses. These organizations must assess internal security by using an “Assumed Breach” mentality.
The SMA will replicate an Assumed Breach on your network. It does this by acting as if an internal endpoint or server is already compromised. It can then act with the assumption that an attacker has gained internal network access.
Sedara manages the SMA setup. This reduces the need for your IT resources to provide additional infrastructure.

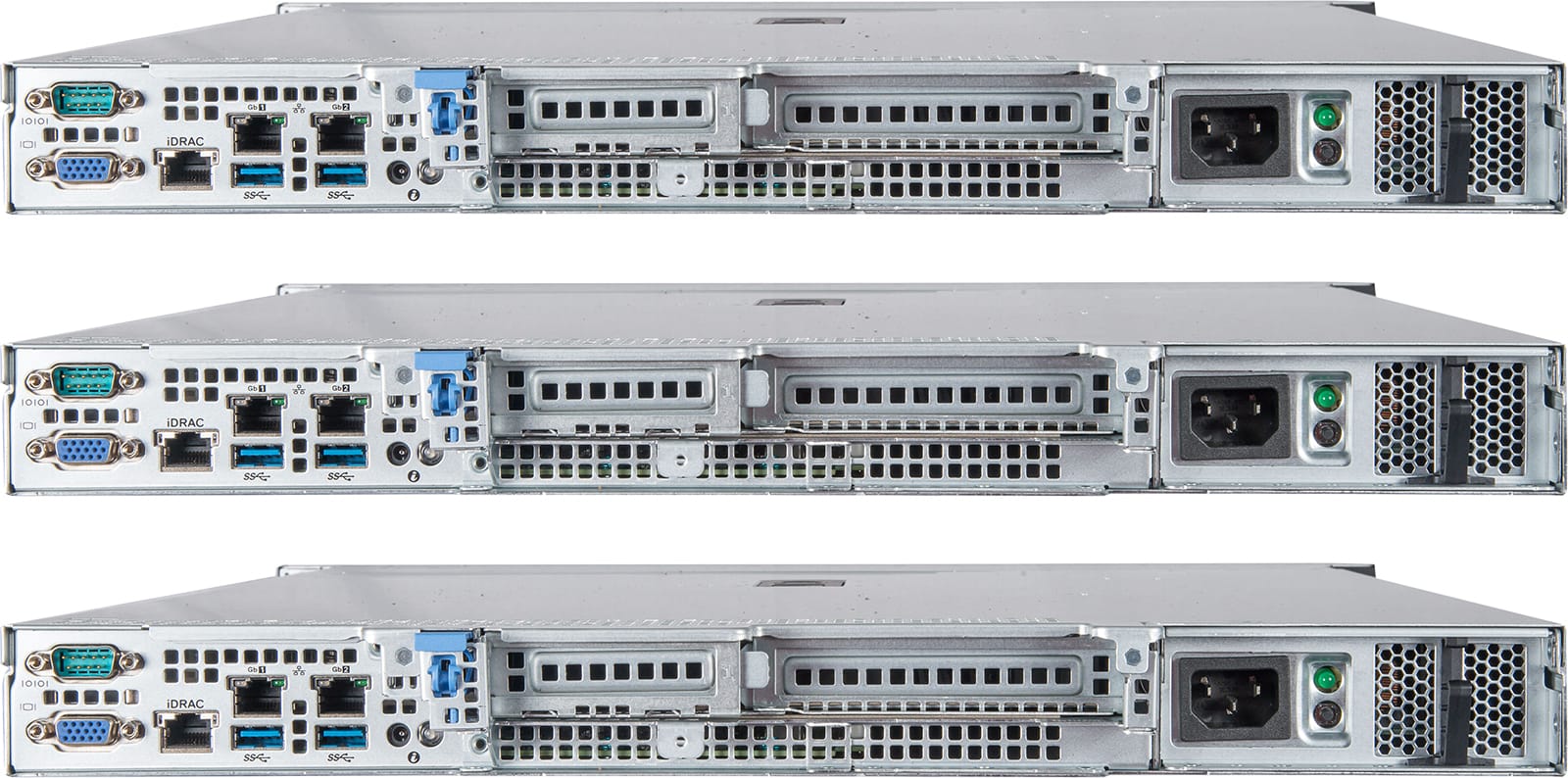
Versatility Meets Scalability
A Linux-based Security Management Appliance is capable in many cybersecurity scenarios:
- Intrusion Detection System (IDS)
- Vulnerability Scanning
- Network Monitoring
- Log Collection and Sensor placement
- Penetration Testing
- Threat Hunting
- Virtual Security Engineering (vSE)
The SMA integrates well with Tenable, Rapid7, Fortinet, and other well known products.
Product Specifications and Comparison
The SMA is scalable for medium, large and global enterprise environments.
These appliances are remotely cloud-managed and meshed.